Protocol Based Intrusion Detection System Diagram
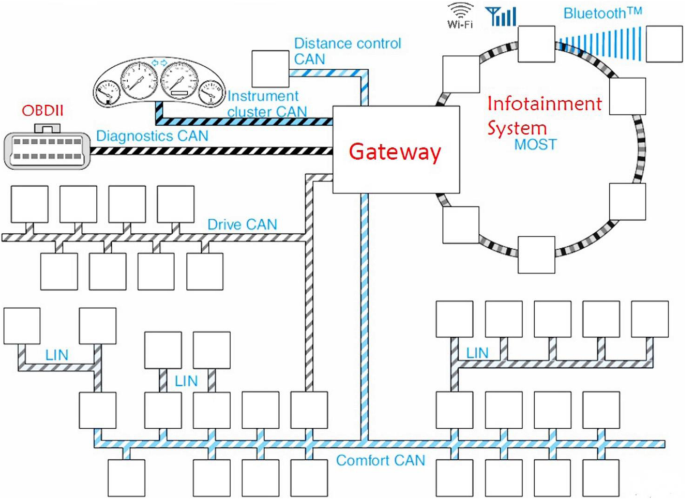
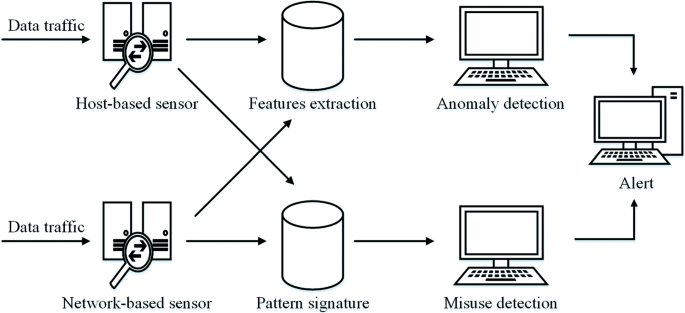
A network based intrusion detection system nids sniffs network traffic packets to detect intrusions and malicious attacks.
Protocol based intrusion detection system diagram. What are two modes of ips. The life expectancy of a default installation of linux red hat 6 2 server is estimated to be less than 72 hours the fastest compromise happened in 15 minutes. What is anomaly based detection. Any intrusion activity or violation is typically reported either to an administrator or collected centrally using a security information and event management siem system.
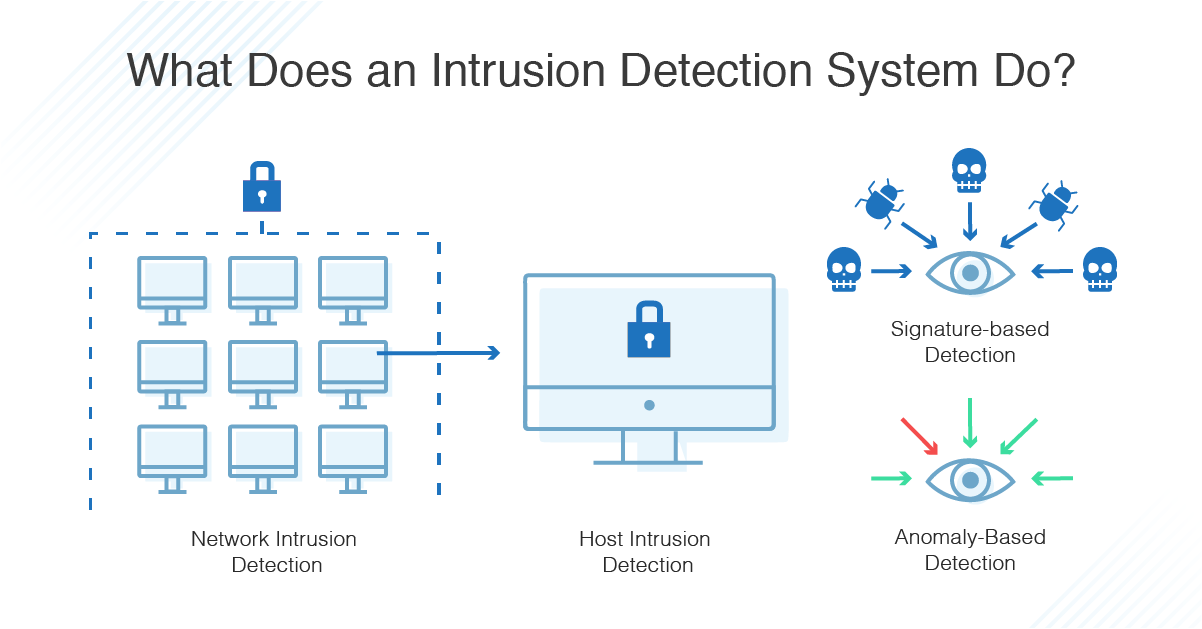
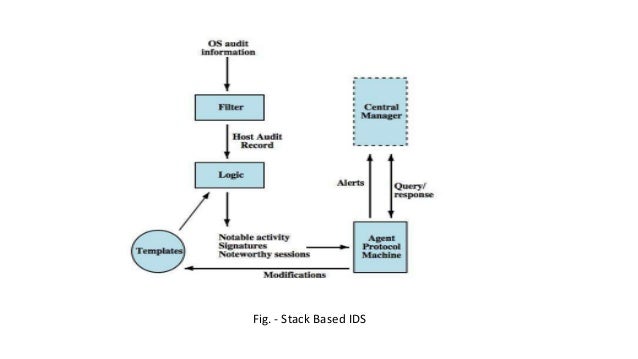
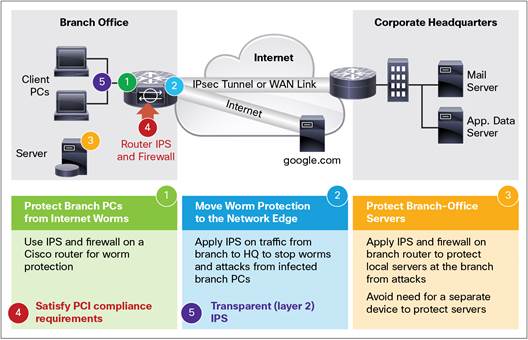
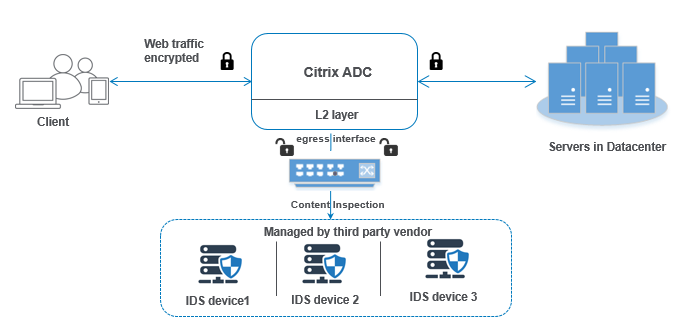
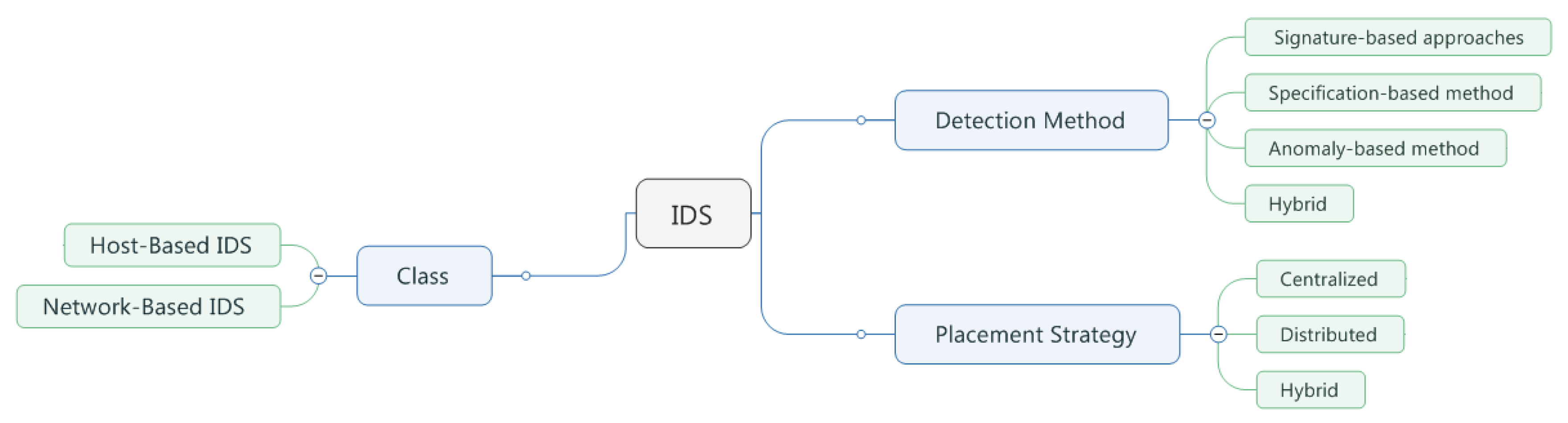
Intrusion detection systems can be grouped into the following categories. For example snort nids is a software based nids. Nids can be hardware or software based systems and depending on the manufacturer of the system can attach to various network mediums such as ethernet fddi and others. Protocol based intrusion detection system pids comprises of a system or agent that would consistently resides at the front end of a server controlling and interpreting the protocol between a user device and the server.
Host based idss are designed to monitor detect and respond to activity and attacks on a given host. The pros and cons of this method are summarized in table 11 5. Network based intrusion detection systems nids are devices intelligently distributed within networks that passively inspect traffic traversing the devices on which they sit. What is inline mode.
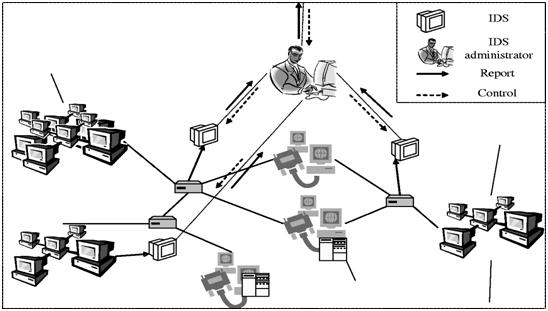
Stateful inspection resource intensive. If the protocol implementation varies from operating system to operating system then idps may not perform well in detecting the intrusions. It is trying to secure the web server by regularly monitoring the https protocol stream and accept the related http protocol. The operational structure of a nids and its location in the network are shown in fig.
A nids can be either a software based system or a hardware based system. What is intrusion detection intrusion detection systems idss are designed for detecting blocking and reporting unauthorized activity in computer networks. A protocol based intrusion detection system pids is an intrusion detection system which is typically installed on a web server and is used in the monitoring and analysis of the protocol in use by the computing system. What is importance of intrusion detection system ids.
What is promiscuous mode. What is the mode of the ips from the diagram below. What is signature based detection. Intrusion prevention system ips host based intrusion detection systems.
Designing and deploying intrusion detection systems. Remote data exchange protocol xml based communications protocol between sensors and management apps encrypted using ssl event and transaction message entity bodies consist of xml documents. Where ips devices are usually deployed in a network. Acceptable protocol behavior then it can pass through.
Name few of the vendor who deals in ips ids.